(单词翻译:单击)
I'm a computer science professor, and my area of expertise is computer and information security.
我是一个计算机科学教授,我的专业领域是计算机与信息安全。
When I was in graduate school, I had the opportunity to overhear my grandmother describing to one of her fellow senior citizens what I did for a living.
当我还在研究生院的时候,我有次听见了我祖母向她的一位高龄同乡描述我的工作。
Apparently, I was in charge of making sure that no one stole the computers from the university.
没想到,她说我的工作是确保学校的计算机不被小偷偷走。
And, you know, that's a perfectly reasonable thing for her to think,
但你也会觉得她这么想是完全合理的,
because I told her I was working in computer security, and it was interesting to get her perspective.
因为我告诉她我工作内容是计算机安全,但是能够得知她的观点真的很有趣。
But that's not the most ridiculous thing I've ever heard anyone say about my work.
但这并不是我所听过对我工作最离谱的叙述。
The most ridiculous thing I ever heard is, I was at a dinner party, and a woman heard that I work in computer security,
我听过最谱奇的版本是,我在一个晚宴上,然后有一位女士听说我是负责计算机安全的,
and she asked me if -- she said her computer had been infected by a virus,
于是她问我如果--她的电脑感染了病毒,
and she was very concerned that she might get sick from it, that she could get this virus.
所以她十分担心自己会因此而生病,会感染到这个病毒。
And I'm not a doctor, but I reassured her that it was very, very unlikely that this would happen,
虽然我不是个医生,但我向她再三保证这种事不可能会发生,
but if she felt more comfortable, she could be free to use latex gloves when she was on the computer,
但如果她还是不放心,她或许可以考虑在用电脑的时候带着橡胶手套,
and there would be no harm whatsoever in that.
而且这无论如何都是无害的。
I'm going to get back to this notion of being able to get a virus from your computer, in a serious way.
我一会儿会回过头来谈谈这种能够被自己电脑的病毒感染的想法,用一个更严肃的角度来谈。
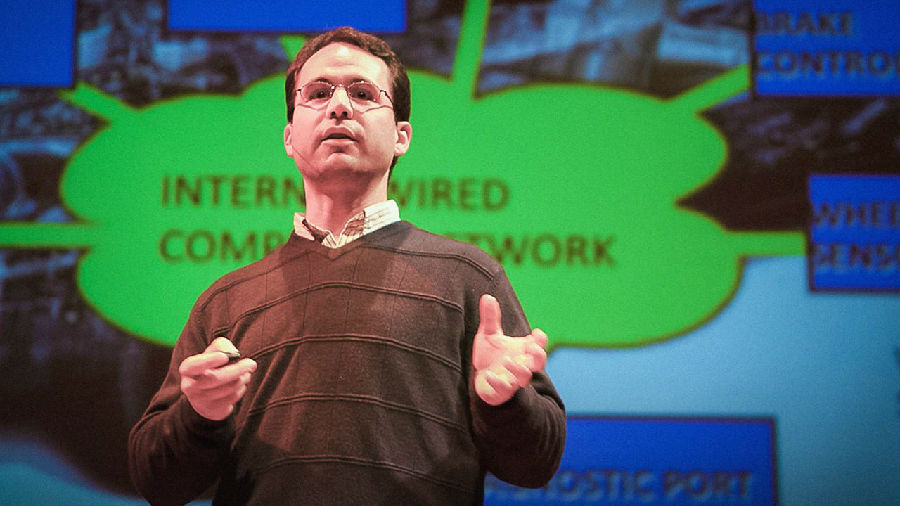
What I'm going to talk to you about today are some hacks, some real world cyberattacks
今天我要讲的是一些黑客活动和一些真实世界的网络攻击,
that people in my community, the academic research community, have performed, which I don't think most people know about,
它们是我的领域--学术研究界--的人员所进行的、为大多人所不知的,
and I think they're very interesting and scary, and this talk is kind of a greatest hits of the academic security community's hacks.
我觉得它们既有意思又可怕,而这次的演说就有点像是学术的安全共同体中的经典黑客案例。
None of the work is my work.
这些都不是我个人的工作。
It's all work that my colleagues have done, and I actually asked them for their slides and incorporated them into this talk.
这全部都是我同事做的,而我其实还向他们要了一些幻灯片,并把它们加到我的演讲里。
So the first one I'm going to talk about are implanted medical devices.
那么,我要讲的第一个案例就是植入性医疗器械。
Now medical devices have come a long way technologically.
当今的医疗器械是经历了一段很长的科技发展。
You can see in 1926 the first pacemaker was invented.
你可以看到,第一款心脏起搏器发明于1926年。
1960, the first internal pacemaker was implanted, hopefully a little smaller than that one that you see there,
1960年,第一个体内心脏起搏器被植入,希望是比大家在这看到的要小一些,
and the technology has continued to move forward.
之后,这方面的技术一直在不断地发展。
In 2006, we hit an important milestone from the perspective of computer security.
到了2006年,我们迎来了一个对于电脑安全而言很重要的里程碑。
And why do I say that? Because that's when implanted devices inside of people started to have networking capabilities.
那我为什么这么说呢?那是因为这正是植入人体的器械开始具备联网能力的时候。
One thing that brings us close to home is we look at Dick Cheney's device,
一件带我们回主题的事就是当我们看到迪克·切尼的仪器,
he had a device that pumped blood from an aorta to another part of the heart,
他拥有一台可以将血液从一个大动脉输送到心脏的另一个部分的仪器,
and as you can see at the bottom there, it was controlled by a computer controller,
就如你在底部所看到的,它是被一个电脑控制器所控制的,
and if you ever thought that software liability was very important, get one of these inside of you.
如果你认为软件责任非常重大的话,你可以给自己装一个这个。
Now what a research team did was they got their hands on what's called an ICD.
现在有一支研究团队所做的就是得到了一个被称作ICD(植入型心律转复除颤器)的器件。
This is a defibrillator, and this is a device that goes into a person to control their heart rhythm, and these have saved many lives.
这是一个复除颤器,而且这是个用在人体体内来控制他们心率的仪器,而且这仪器还救过不少人的命。
Well, in order to not have to open up the person every time you want to reprogram their device or do some diagnostics on it,
那么,为了不用每次给装置重新编程,或者进行某些其他的检测的时候都要剖开病人的胸腔,
they made the thing be able to communicate wirelessly, and what this research team did is they reverse engineered the wireless protocol,
他们让这个装置可以无线通讯,而这个研究团队所做的就是对无线协议做逆向工程,
and they built the device you see pictured here, with a little antenna, that could talk the protocol to the device, and thus control it.
并制作出你现在所看到的图中所显示的仪器,它还有一个小天线,用于与设备进行交流,从而进行操控。
In order to make their experience real -- they were unable to find any volunteers,
为了让他们的试验更真实--他们无法找到任何志愿者,
and so they went and they got some ground beef and some bacon
所以他们找来一些牛肉馅儿和培根肉,
and they wrapped it all up to about the size of a human being's area where the device would go,
弄成一个大小和人体内安放这个装置差不多大小的区域,
and they stuck the device inside it to perform their experiment somewhat realistically.
然后他们把这个装置放了进去,从而使他们的实验近乎真实。
They launched many, many successful attacks. One that I'll highlight here is changing the patient's name.
他们进行了很多很多成功的攻击。我特别想重点讲一下的是他们成功地修改了病人的姓名信息。
I don't know why you would want to do that, but I sure wouldn't want that done to me.
我不清楚为什么有人要这么做,但是我肯定不愿意有人对我这么做。
And they were able to change therapies, including disabling the device -- and this is with a real, commercial, off-the-shelf device
他们还能够更改治疗方案,包括使设备失效--而这些都发生在一个真的、营利的、市场上能买到的心率仪上,
simply by performing reverse engineering and sending wireless signals to it.
仅仅是通过反向破解以及向其发送无线指令就能实现。
There was a piece on NPR that some of these ICDs could actually have their performance disrupted simply by holding a pair of headphones onto them.
NPR上曾经有过一则新闻报到了一些ICD的运行甚至可以被放在其上面的一副耳机扰乱。
Now, wireless and the Internet can improve health care greatly.
如今,无线技术和互联网能够大大改善医疗服务。
There's several examples up on the screen of situations where doctors are looking to implant devices inside of people,
屏幕上显示的几个例子是一些医生要为病人体内植入医疗装置的情况,
and all of these devices now, it's standard that they communicate wirelessly,
而现今所有这方面的仪器,无线联网已经成为了标准配备,
and I think this is great, but without a full understanding of trustworthy computing,
我认为这很了不起,但是如果没有全面的了解和可靠的计算,
and without understanding what attackers can do and the security risks from the beginning, there's a lot of danger in this.
以及没有认识到攻击行为所造成的影响、固有的安全隐患,这就会带来很多危险。
Okay, let me shift gears and show you another target.
好的,让我换个机械,向你们展示另外一个攻击对象。
I'm going to show you a few different targets like this, and that's my talk. So we'll look at automobiles.
我将向你们展示几个类似的攻击对象,它们是我演讲的主要部分。我们接下来看看汽车。
This is a car, and it has a lot of components, a lot of electronics in it today.
这是一辆车,它拥有很多组成部分,如今还拥有许多的电子零件。
In fact, it's got many, many different computers inside of it,
事实上,它里面有很多很多台不同的电脑,
more Pentiums than my lab did when I was in college, and they're connected by a wired network.
它所拥有的奔腾处理器比我大学时期的实验室里的还多,而且这些电脑之间是由内部线路相连。
There's also a wireless network in the car, which can be reached from many different ways.
车内也有一个无线网络,它可以通过不同的方式与外界相连。
So there's Bluetooth, there's the FM and XM radio, there's actually wi-fi,
包含了蓝牙,有FM广播和XM广播,甚至还有wi-fi,
there's sensors in the wheels that wirelessly communicate the tire pressure to a controller on board.
车轮里面有传感器,可以通过无线网络监测轮胎气压并传输给控制板。
The modern car is a sophisticated multi-computer device.
现代汽车是非常复杂的多电脑设备。
And what happens if somebody wanted to attack this?
那如果有人想攻击这台设备的话会发生什么呢?
Well, that's what the researchers that I'm going to talk about today did.
这就是今天我演讲中的研究者们所做的。
They basically stuck an attacker on the wired network and on the wireless network.
他们在汽车的有线和无线网络上都安装了攻击装置。
Now, they have two areas they can attack.
现在,他们可以通过两种方式进行攻击。
One is short-range wireless, where you can actually communicate with the device from nearby,
一种是短程无线网络,这样你可以直接和附近的装置进行通信,
either through Bluetooth or wi-fi, and the other is long-range,
比如通过蓝牙或wi-fi,另一个是远程网络,
where you can communicate with the car through the cellular network, or through one of the radio stations.
让你可以通过移动网络,或者通过某个无线电电台与车进行通信。
Think about it. When a car receives a radio signal, it's processed by software.
想想看。当一辆汽车接收到无线电信号,软件会对这信号进行处理。
That software has to receive and decode the radio signal, and then figure out what to do with it,
该软件必需对信号进行接收和解码,从而弄明白如何进行处理,
even if it's just music that it needs to play on the radio, and that software that does that decoding,
即便那只是电台音乐,而那进行解码的软件,如果存有任何漏洞,
if it has any bugs in it, could create a vulnerability for somebody to hack the car.
就有机会让他人入侵汽车的电脑系统中。
The way that the researchers did this work is, they read the software in the computer chips that were in the car,
研究人员试验的方法就是,他们读取了车内电脑芯片中的软件,
and then they used sophisticated reverse engineering tools to figure out what that software did,
之后他们运用复杂的反向破解工具,来弄明白了这个软件的功能,
and then they found vulnerabilities in that software, and then they built exploits to exploit those.
并且找到了软件的漏洞,之后他们利用这些漏洞建造后门。
They actually carried out their attack in real life.
他们真的在现实生活中试验了这些攻击。
They bought two cars, and I guess they have better budgets than I do.
他们买了两辆车,我猜他们的经费比我要宽裕一些。
The first threat model was to see what someone could do if an attacker actually got access to the internal network on the car.
第一个攻击计划是想看看一个人能在攻击者得到许可进入汽车的内部网络时做些什么。
Okay, so think of that as, someone gets to go to your car, they get to mess around with it,
好的,假设有一个人可以接近你的车,在车中做了一些手脚,
and then they leave, and now, what kind of trouble are you in?
然后离开,那现在,你会遇到些什么麻烦呢?
The other threat model is that they contact you in real time over one of the wireless networks like the cellular, or something like that,
另一个计划是他们通过无线网络进行实时交流,就像手机或是其他类似的方式,
never having actually gotten physical access to your car.
根本不需要跟你的车有任何的物理上的接触。
This is what their setup looks like for the first model, where you get to have access to the car.
这是他们第一个模型设置的样子,在这儿他们可以接触到车。
They put a laptop, and they connected to the diagnostic unit on the in-car network,
他们放了一个笔记本电脑,并把它连接到车内部网络的诊断单元,
and they did all kinds of silly things, like here's a picture of the speedometer showing 140 miles an hour when the car's in park.
他们利用这些做了各种各样好玩的把戏,像这张车速表的照片,在车静止的情况下显示每小时140英里。
Once you have control of the car's computers, you can do anything.
当你控制住车内电脑系统,你可以做任何事。
Now you might say, "Okay, that's silly."
你也许会觉得,“这只是搞笑而已。”
Well, what if you make the car always say it's going 20 miles an hour slower than it's actually going?
那如果你让车总是显示比真正的速度慢了20英里每小时呢?
You might produce a lot of speeding tickets.
这样会拿到很多超速罚单。
Then they went out to an abandoned airstrip with two cars,
之后他们开了两辆车到一个废弃的简易机场,
the target victim car and the chase car, and they launched a bunch of other attacks.
一辆目标车,一辆追踪车,他们进行了更多其他的攻击。
One of the things they were able to do from the chase car is apply the brakes on the other car, simply by hacking the computer.
其中一件可以从追踪车里做到的事,就是在目标车中进行刹车,这只需要侵入目标车的电脑就可以了。
They were able to disable the brakes. They also were able to install malware that wouldn't kick in and wouldn't trigger
他们可以废掉刹车系统。他们还能够安装恶意软件,通常情况下这个软件不会被触发,
until the car was doing something like going over 20 miles an hour, or something like that.
直至如车辆时速超过每小时20英里,或类似的情况。
The results are astonishing, and when they gave this talk,
这个结果非常的震撼,而当他们做这个演讲时,
even though they gave this talk at a conference to a bunch of computer security researchers, everybody was gasping.
即使是在一个充满电脑安全研究人员的会议中,所有人都难以置信。
They were able to take over a bunch of critical computers inside the car:
他们成功的控制了车内很多重要的电脑系统:
the brakes computer, the lighting computer, the engine, the dash, the radio, etc.,
刹车系统、照明系统、发动机、仪表盘、无线电台等等,
and they were able to perform these on real commercial cars that they purchased using the radio network.
而且他们可以在他们所购买的商务车中利用无线网络来做这些事情。
They were able to compromise every single one of the pieces of software that controlled every single one of the wireless capabilities of the car.
他们能够攻击车上每一个带有无线功能的模块软件的任何一部分。
All of these were implemented successfully.
所有的实验都成功实施了。
How would you steal a car in this model?
你要怎样去偷这类型的车呢?
Well, you compromise the car by a buffer overflow of vulnerability in the software, something like that.
首先你从内部软件缓冲区溢出的漏洞开始侵入,就像这样。
You use the GPS in the car to locate it.
你再用车内置的导航器确定它的位置。
You remotely unlock the doors through the computer that controls that, start the engine, bypass anti-theft, and you've got yourself a car.
之后你通过电脑遥控打开车门,启动发动机,绕过防盗系统,这样你就弄到了一辆车。
Surveillance was really interesting.
监控是很有意思的。
The authors of the study have a video where they show themselves taking over a car and then turning on the microphone in the car,
这个研究的作者们有一个影像显示他们侵入一辆车,然后打开车内的话筒,
and listening in on the car while tracking it via GPS on a map,
听着车内的声音,并同时用导航器跟踪车的位置,
and so that's something that the drivers of the car would never know was happening.
而这些是车的司机绝对不会知道的。
Am I scaring you yet? I've got a few more of these interesting ones.
我吓到你们了吗?我还有几个很有趣的实验。
These are ones where I went to a conference, and my mind was just blown, and I said, "I have to share this with other people."
这些是我从一个我去过的会议所知道的,我当时惊呆了,我说,“我得跟其他人分享这个信息。”
This was Fabian Monrose's lab at the University of North Carolina,
这是Fabian Monrose在北卡罗莱纳大学的实验室,
and what they did was something intuitive once you see it, but kind of surprising.
他们研究的是你看到的直观的普通事物,但结果是令人惊讶的。
They videotaped people on a bus, and then they post-processed the video.
他们在公共汽车上对人进行录像,然后进行后期处理。
What you see here in number one is a reflection in somebody's glasses of the smartphone that they're typing in.
你在这里看到的第一个图,是在某个人的眼镜中反射的智能手机在打字的图像。
They wrote software to stabilize -- even though they were on a bus
他们用软件以稳定--即使他们是在公共汽车上(来回晃动),
and maybe someone's holding their phone at an angle to stabilize the phone, process it,
或者有人在一个角度拿着自己的手机稳定电话图像,处理图像,
and you may know on your smartphone, when you type a password, the keys pop out a little bit,
然后你可能知道了,在你的智能手机上,当你输入一个密码,字母会弹出一会儿,
and they were able to use that to reconstruct what the person was typing, and had a language model for detecting typing.
然后他们就能用它来重建刚才输入的信息,并且他们有一个语言模型。
What was interesting is, by videotaping on a bus, they were able to produce exactly what people on their smartphones were typing,
很有趣的是,通过在公共汽车上录像,他们能够精确地得知人们在他们的智能手机打的字,
and then they had a surprising result, which is that their software had not only done it for their target,
然后他们有一个惊人的结果,软件不仅完成对目标的监控分析,
but other people who accidentally happened to be in the picture, they were able to produce what those people had been typing,
而且也把碰巧出现在图像中的其他人的打字输入也分析出来了,
and that was kind of an accidental artifact of what their software was doing.
这是他们的软件的一个意外的收获。
I'll show you two more. One is P25 radios.
我再给你们展示两个例子。一个是P25无线电通话机。
P25 radios are used by law enforcement and all kinds of government agencies and people in combat to communicate,
P25无线电是执法部门和各种政府机构,以及战场上的人们交流所使用的。
and there's an encryption option on these phones. This is what the phone looks like.
而且这些手机有个加密选项。这是就是P25无线电通话机。
It's not really a phone. It's more of a two-way radio.
这不是一个真正的电话。这是一个双向无线电。
Motorola makes the most widely used one, and you can see that they're used by Secret Service,
使用得最广泛的是由摩托罗拉所制造的,你可以看到,秘密机构在使用它,
they're used in combat, it's a very, very common standard in the U.S. and elsewhere.
他们在战斗中使用它,在美国和其他地方,这是一个非常普遍的标准装备。
So one question the researchers asked themselves is, could you block this thing, right?
因此,研究人员自问的一个问题就是,你能否屏蔽这个东西呢?
Could you run a denial-of-service, because these are first responders?
可以执行拒绝服务吗,因为这些都是第一反应人员。
So, would a terrorist organization want to black out the ability of police and fire to communicate at an emergency?
所以,在紧急情况下,一个恐怖组织会不会黑掉警察和消防的通讯能力?
They found that there's this GirlTech device used for texting that happens to operate at the same exact frequency as the P25,
他们发现,有一个GirlTech公司的设备可以用来发短信,工作频率和P25完全相同,
and they built what they called My First Jammer. If you look closely at this device, it's got a switch for encryption or cleartext.
于是他们就用这个东西建立了他们所称的“我的第一个干扰器”。如果你仔细观察此设备,它有一个开关,用于设定加密发送或明文发送。
Let me advance the slide, and now I'll go back. You see the difference?
让我前进一下幻灯片,现在我再翻回去。你看到其中的差别了吗?
This is plain text. This is encrypted. There's one little dot that shows up on the screen, and one little tiny turn of the switch.
这是纯文本。这是加密的。有一个小点,显示在屏幕上,还有一个小的转换开关。
And so the researchers asked themselves,
因此,研究人员问自己,“
"I wonder how many times very secure, important, sensitive conversations are happening on these two-way radios
我不知道有多少次,非常机密的、重要的、敏感的对话,发生在这些双向无线电设备上,
where they forget to encrypt and they don't notice that they didn't encrypt?"
他们忘了加密,并且他们没有注意到在进行未加密的通话吗?”
So they bought a scanner. These are perfectly legal and they run at the frequency of the P25,
于是,他们买了一台无线电扫描设备。这是完全合法的,然后他们运行在P25的频段上,
and what they did is they hopped around frequencies and they wrote software to listen in.
然后他们在附近的频段上跳来跳去的扫描,他们写软件监听。
If they found encrypted communication, they stayed on that channel and they wrote down,
如果他们发现加密的通信,他们就停留在该频道上,记下来,
that's a channel that these people communicate in, these law enforcement agencies,
这是一个执法机构的人们在通话的频道,
and they went to 20 metropolitan areas and listened in on conversations that were happening at those frequencies.
然后他们去了20个大都市地区,在这些频率上监听。
They found that in every metropolitan area, they would capture over 20 minutes a day of cleartext communication.
他们发现,在每一个大都市区,每天他们将捕获超过20分钟的明文通信。
And what kind of things were people talking about?
那他们都交流些什么呢?
Well, they found the names and information about confidential informants.
他们得到了秘密举报人的名字和信息。
They found information that was being recorded in wiretaps, a bunch of crimes that were being discussed, sensitive information.
他们得到了正在被窃听的信息,一堆正在被讨论的犯罪案件,敏感的消息。
It was mostly law enforcement and criminal.
大多数都是执法和犯罪类的。
They went and reported this to the law enforcement agencies, after anonymizing it,
他们向执法机构说明了这件事,当然是在匿名之后,
and the vulnerability here is simply the user interface wasn't good enough.
而当中的漏洞很纯粹的只是用户界面不够好。
If you're talking about something really secure and sensitive,
如果你是在讨论一些非常保密或者敏感话题,
it should be really clear to you that this conversation is encrypted. That one's pretty easy to fix.
你应该清楚的知道这个谈话是被加密的。这个很容易修正。
The last one I thought was really, really cool, and I just had to show it to you,
最后一个例子我认为是非常、非常的酷,所以我必须得给你们看这个,
it's probably not something that you're going to lose sleep over like the cars or the defibrillators, but it's stealing keystrokes.
这可能不是一些会使你们失眠的东西,像是汽车实验和心脏去颤器那样,但它可以窃取按键信息。
Now, we've all looked at smartphones upside down.
现在,我们上下颠倒着看一下智能手机。
Every security expert wants to hack a smartphone, and we tend to look at the USB port, the GPS for tracking, the camera, the microphone,
每个安全专家都想要侵入这样的手机系统,而我们一般都会去看USB插头,跟踪GPS,相机,话筒,
but no one up till this point had looked at the accelerometer.
但目前为止没有人看过加速度计。
The accelerometer is the thing that determines the vertical orientation of the smartphone. And so they had a simple setup.
加速度计是那个决定手机垂直方向的东西。因此他们有个很简单的设置。
They put a smartphone next to a keyboard, and they had people type,
他们把手机放在键盘旁边,然后让人们去打字,
and then their goal was to use the vibrations that were created by typing to measure the change in the accelerometer reading
而他们的目标是利用打字而产生的震动,去测量加速度计的数据的变化,
to determine what the person had been typing.
由此来判断这个人输入的是什么。
Now, when they tried this on an iPhone 3GS, this is a graph of the perturbations that were created by the typing,
那么当他们在用iPhone 3GS做该实验时,这是他们从打字所得到的图形的摄动,
and you can see that it's very difficult to tell when somebody was typing or what they were typing,
你可以看到,很难确认人在什么时候打字和他们打字的内容,
but the iPhone 4 greatly improved the accelerometer, and so the same measurement produced this graph.
但是iPhone 4在加速度计上有很大的提高,因此同样的测量所得到的图是这样的。
Now that gave you a lot of information while someone was typing,
现在,当有人打字的时候,这个图会给你提供大量信息,
and what they did then is used advanced artificial intelligence techniques called machine learning to have a training phase,
他们接下来用了一个先进的、被称为“机器学习”的人工智能技术,来进行训练阶段,
and so they got most likely grad students to type in a whole lot of things,
然后他们极有可能是找了一些研究生去输入一大堆的东西,
and to learn, to have the system use the machine learning tools that were available to learn what it is that the people were typing
然后去学习,让这个系统利用已有的机器学习工具,去了解这些人输入的是什么,
and to match that up with the measurements in the accelerometer.
并结合了加速度计所测量的数据。
And then there's the attack phase, where you get somebody to type something in, you don't know what it was,
接下来就是攻击阶段了,你找一些人来输入一些东西,但是你不知道输入的是什么,
but you use your model that you created in the training phase to figure out what they were typing.
但你利用之前在培训中所编写的模式来得出输入的内容。
They had pretty good success. This is an article from the USA Today.
他们有很高的成功几率。这是一篇出自《今日美国》的文章。
They typed in, "The Illinois Supreme Court has ruled that Rahm Emanuel is eligible to run for Mayor of Chicago"
他们输入了“伊利诺伊州最高法院裁定伊曼纽尔拥有参加芝加哥市长竞选的资格”,
see, I tied it in to the last talk — "and ordered him to stay on the ballot."
看,我把它绑在最后一次谈话“并命令他继续竞选”。
Now, the system is interesting, because it produced "Illinois Supreme" and then it wasn't sure.
这个系统很有趣,因为它分析出了“伊利诺伊州最高”,而之后的它就不确定了。
The model produced a bunch of options, and this is the beauty of some of the A.I. techniques,
这个模式给了一堆的选择,这也就是人工智能技术厉害的地方,
is that computers are good at some things, humans are good at other things, take the best of both and let the humans solve this one.
也就是电脑在某方面很在行,而人类则是在别的方面很强,结合双方的优势,并让人类去解决这一个问题。
Don't waste computer cycles. A human's not going to think it's the Supreme might.
不要浪费计算机的运算。一个人不会认为这是“Supreme might”。
It's the Supreme Court, right? And so, together we're able to reproduce typing simply by measuring the accelerometer. Why does this matter?
当然是“Supreme Court”,对吧?所以,我们能够简单地通过测量加速度计来重现输入。为什么这个事情很重要呢?
Well, in the Android platform, for example, the developers have a manifest where every device on there, the microphone, etc.,
好吧,用安卓平台来举个例子,开发者们有一个清单,当中的每一个设备,像是麦克风等等,
has to register if you're going to use it so that hackers can't take over it, but nobody controls the accelerometer.
如果你要使用它就必须注册,这样黑客就无法接管,但没有人控制加速度计。
So what's the point? You can leave your iPhone next to someone's keyboard, and just leave the room,
那重点是什么呢?你可以把你的iPhone放在某人的键盘旁边,然后就离开房间,
and then later recover what they did, even without using the microphone.
之后再回来复原他们所做过的事,就连麦克风都不需要。
If someone is able to put malware on your iPhone,
如果有人能够把入侵软件装入你的iPhone,
they could then maybe get the typing that you do whenever you put your iPhone next to your keyboard.
那么每当你把你的iPhone放在你的键盘旁边时,他们也就可能得到你所输入的内容。
There's several other notable attacks that unfortunately I don't have time to go into,
另外还有几个值得注意的攻击,但很不幸,我没有时间去说了,
but the one that I wanted to point out was a group from the University of Michigan which was able to take voting machines,
但有一个我想点出的,是在密歇根大学的一组人员,他们成功的侵入了投票机,
the Sequoia AVC Edge DREs that were going to be used in New Jersey in the election
这是Sequoia AVC Edge DRE(美国最大的电子投票机制造商之一)准备在新泽西州选举中用的,
that were left in a hallway, and put Pac-Man on it. So they ran the Pac-Man game.
它被留在了一个走廊里,里面安装了吃豆人游戏。他们运行了吃豆人游戏。
What does this all mean? Well, I think that society tends to adopt technology really quickly.
这些都有什么意义呢?我觉得我们的社会往往很快的采用新技术。
I love the next coolest gadget. But it's very important, and these researchers are showing,
我非常喜欢下一个最炫的小玩意儿。但是更重要的是,这些研究人员所表明的,
that the developers of these things need to take security into account from the very beginning,
这些东西的开发者需要从一开始就把安全考虑在内,
and need to realize that they may have a threat model,
也需要意识到它们可能会有一个威胁模型,
but the attackers may not be nice enough to limit themselves to that threat model, and so you need to think outside of the box.
但是那些攻击者也许不会好心到只把他们局限于这些威胁模型中,所以你需要跳脱传统思维。
What we can do is be aware that devices can be compromised, and anything that has software in it is going to be vulnerable.
我们所能做得就是要意识到设备是可以被攻击的,而任何有软件的东西都是会有弱点的。
It's going to have bugs. Thank you very much.
它们是会有漏洞的。非常感谢。